Securing the laptops that schools give to children
Posted on 2024-05-27 by Matt Strahan in Business Security
This week Alexei and I will be presenting at the AISNSW ICT Management and Leadership Conference. Alexei is giving workshops on physical security and going from on-prem active directory to cloud based Microsoft 365. I’ll be presenting on Essential 8 for schools, why they might use it and what it’s trying to protect.
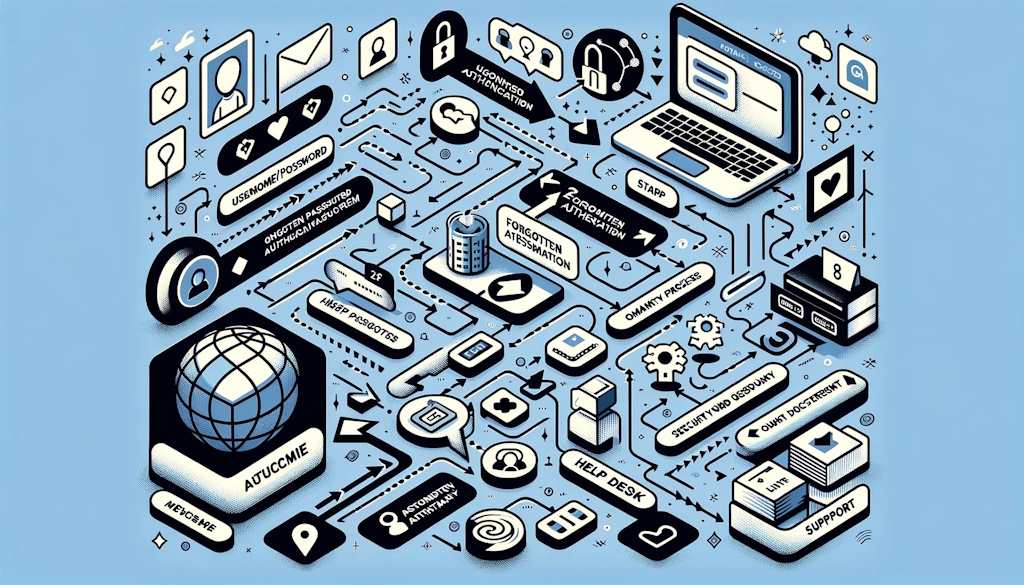
A while ago I talked about how healthcare has extremely specific security requirements and limitations around how they can approach security. Really, though, every industry faces their own unique challenges. For schools, they have the rather unique requirement of having to provision and secure devices that are going to be used by children. Imagine asking a primary school child, for example, to get out their phone and type in a multi-factor authentication code to get access to their learning platform? The way of “locking down” their systems must be approached in a very different way to enterprises.
In this post I’ll be giving my opinion on it. There’s no “right way” to secure the laptops of school kids and even amongst individual schools they may have to have different approaches for different year groups, but hopefully I can give out some ideas.