Posted on 2022-10-05 by Nathan Jarvie in Industry
This is the first part of a 5 part series in which I will walk through the decision making process and the steps involved in transitioning from a system administrator to a penetration tester. The certifications taken and the the issues and obstacles that I faced along the way.
This is my story, and I hope it helps to inspire people who are considering a mid-life career change that it is possible to do so and to take the leap.
Introduction
My name is Nathan Jarvie, I also go by the handle Kinryu on various social media platforms and games. You can catch me on LinkedIn and Twitter.
I have over 10 years of IT experience, including 9 years as a Systems and Network engineer, and eventually a manager at an MSP. I have just celebrated my first anniversary of changing careers into penetration testing with Volkis.
I am also a parent, a husband, a casual ballroom dancing instructor and a passionate (but average) snowboarder and gamer.

I recently presented a talk at ComfyCon 2022 where I shared my story about changing careers into penetration testing in my 30’s. I discussed what challenges I faced, and what I have learned since starting this wonderful job, that I wish I had known beforehand. As is natural for a con talk, I was not able to go into the amount of detail I would have liked within the time limit, and have received more than a few requests to post up a blog. So here it is!
The talk itself can be found below. Please excuse the poor mic quality, I will have to invest in a new one. Also my slides didn’t work, but that’s another story.
I have put together this multi-part blog post for anyone who is looking to find a leg-up into the InfoSec industry. I share my story of how I got into pentesting, for those who are interested, and more importantly for you, the lessons I have learned that can help you to stand out in the super-competitive junior InfoSec job-seeker market.
I also cover the certifications and courses I have completed that I have considered a valuable investment of your time and money. For now I will leave off the certifications that aren’t worth your effort, but I will come back to them another day if there is interest.
Finally, I provide a direct comparison of TCM Security’s Practical Network Penetration Tester (PNPT) and Offensive Security Certified Professional (OSCP) courses and exams.
It probably goes without saying but for the sake of clarity: The content in the following pages are my own opinions and experiences, and may not be relevant to everyone. But I hope you enjoy the ride and find something valuable in these pages.
From SysAdmin to Pentester in about 1 million steps
My IT Journey started in 2012. I had just completed a Diploma of Information Technology at RMIT, and was working full-time in computer sales at a retail giant. I was lucky enough to be referred by a family member to a business looking for a junior support technician. They took a chance on me and I got my start in the IT industry.
Fisher-Price - My first career
The company is a niche MSP in Melbourne who specialised in Mac and cross-platform environments for small-medium businesses. As is expected when working with smaller clients, the IT consultants responsible for keeping the systems running need to be versed in all aspects of IT. They become the one-stop-shop for anything related to a computer. The work was varied and challenging, covering system administration, troubleshooting, networking, web, security, engineering, project and risk management… the list goes on.
After a couple of years, once the imposter syndrome started to wear down and I got more comfortable in the role, I started getting a feel for what I really enjoyed doing, and what I did because I had to. I liked talking to people, and helping them where I could, to understand the world of technology that is foreign to them. This often happened after a problem was resolved and the stress levels had dropped a bit, but it was the most rewarding part of the job.
The thing that bothered me most is that we were always coming in AFTER the problem had occurred. While some issues were unavoidable or unpredictable, many were not; and as such I developed an interest in IT security. I was interested in how it worked, how our clients were vulnerable and what could be done to protect them.
I can haz security?
I would raise the issue of security with my clients, remembering here that they are small-medium businesses with small IT budgets, and each time I was met with some variant of:
- “We’re too small to be hacked” - Not true
- “No one would target us, we’re not important” - Also not true
- “Macs don’t get viruses, so we’re good” - Definitely not true
- “If we get hacked, I’ll just close up shop and start a new business” - Hilarious, but also not true
Over the years I had to deal with quite a few security-related incidents. Clients getting ransomware, some had backups, some didn’t, what feels like a million phishing and mail-server compromises, and still other clients dealing with internal sabotage or embezzling. Each time, I fixed the issue as best I could, there was often a round of thanks, then I was politely pushed out the door. Clients were often not interested in fixing the root problem, just getting back to work. I was constantly shocked and confused by how little these businesses seemed to care about their security.
The problem, as I discovered, was not that they didn’t care. The issue was that I could not explain why they should secure their systems in a way they understood. The threats faced by being on the Internet were always someone else’s problem, until after an incident had already occurred. When the inevitable incident did occur, the business would spend a considerable sum on remediation, and then, did not have the budget for additional protections against what might happen in the future.
This cycle was problematic, and I struggled to help my clients find a way out of the situation because I barely understood it myself. I was frustrated to say the least. I wanted to learn more and do more to help them.
I raised this with my manager at the time and was promptly shut down. As we were a small team, we all had a role to play and we already had someone who knew about security (him) so there wasn’t a lot of reason for me to pursue it.
To placate me somewhat, he enrolled me in a vendor provided online course that would teach me to use some of the equipment we installed. This was boring as hell and didn’t help me to explain to clients why security was important for them. It was just vendor Kool-Aid. Perhaps this was my fault in not articulating exactly what I wanted to learn, but how could I when I didn’t know enough myself?
Ok, time for big boy pants
After a few more years in the role with no real career progression (though that is no fault of the business; small businesses often have limited progression), my frustrations hit their peak. My manager had recently left the company leaving me and a colleague, being the most senior engineers in the company now, to pick up the slack. We had to quickly learn about all the things we “didn’t need to know about” previously. Both my colleague and I managed to keep ourselves afloat (barely) but we quickly realised that, despite having several years of experience at this point, there were significant gaps in our knowledge and training. When we regained our footing and everything stabilised again, I considered my future and decided that this role was no longer for me. While there was still much to learn, I would never be able to learn more than the surface level content as a jack-of-all-trades System Administrator.
So, in 2019, while in the delivery room waiting for my second child to make an appearance (it was a long one… there was time for this…), I was venting to my wife about my frustrations. She told me what all supportive partners and family say in this situation:
“Then get off your ass and go do something else.”
I explained that moving to a new role would likely mean a stepping down in seniority. “So what? We’ll survive,” she said. And then there was no longer a point in arguing.
Over the course of the next couple of weeks, while on paternity leave, around helping my wife juggle with a newborn child and a 4 year old, I did some research into Cyber Security roles. What are they and what do they do? Which one would suit me? It was overwhelming to realise just how little I knew about security and the possible roles that exist. From SOC analysts to threat modelling, GRC to pentesting. I had no idea what I wanted to do.
I bought a generic “Get into cyber security” course from an education provider that claimed they would get me the “skills and certifications required to get into the role I wanted,” and help me to get a job in the field. It sounded like a dream come true (or possibly a scam), if only I knew what I wanted to do.
So I paid the not-insignificant-sum-of-money, out of my own pocket, and I committed to it. Every single day I would put in some hours of study around full time work, a new born child, a 4 year old, and my side-job. I had no social life for a long time, but what I did get is confidence, and reassurance that this was the right path for me.
The course initially worked through the CompTIA path; I completed my Network+ and Security+ within the first few months. I was then presented with 2 possible options for my next certification: Cyber Security Analyst (CySA+) or Pentester (Pentest+).
Red pill or Blue pill? - Down the rabbit hole…

I worked through the materials for both courses and achieved both certifications. This was possibly the best thing I could have done as it helped me to decide what I actually enjoyed doing. I also dabbled in CISSP content and toyed with the idea of getting that certification, but… that was not for me. I had a lot of fun working through the Pentest+ content so I decided to head down the offensive security path.
I had a distinct advantage over many students; I was already working in the IT industry. While studying I was able to apply my knowledge at work to real world situations and environments. I could discuss with my clients about the security risks they face and the efforts that can be made to mitigate them. As a senior technician I had gained some influence within the team, and I made changes around the office in terms of attitude towards security; bringing it up regularly so that others would consider it when making decisions. I was eventually promoted to Technical Manager and was in charge of the whole team (it was a small team, don’t get excited).
After 2 years I completed the course, which for a pentester meant I had to complete EC-Council’s Certified Ethical Hacker additionally I applied for and was granted a scholarship to complete the practical component of the certification to upgrade the certification. 2 years of study to get from what was effectively 0 knowledge to CEH. I figured now that I was a “Certified Ethical Hacker” I was ready to take on a new challenge.
I started looking for work in the field. I would spend every other evening looking for pentester roles, but every job listing was for a senior tester. Minimum 5 years experience, must have OSCP, must have Crest, etc.
I didn’t have 5 years of experience as a pentester. I didn’t have OSCP. I wasn’t prepared to drop another AU$2000 for another certification that might get me an interview.
Despite having years of IT experience under my belt and the title of “Technical Manager” to boot, it still took over 60 applications before I got my first interview. It was another 20 before I got a job offer, which I had to refuse as it meant relocating my family to another state. I kept applying and was continually rejected at the gate. I was about to put a pin in it and see about trying for a different role when I got my dream interview.
Success!! Oh shi-
I had to go through multiple interviews; there was competition which is not surprising for entry-level roles who are looking for actual entry-level candidates, but ultimately I was successful in getting a role as an Associate Security Consultant at Volkis.
I remember it was a bittersweet moment as I would be leaving my old job, which while frustrating, was comfortable. I loved the people I worked with; it was going to be sad saying goodbye. I was also stepping down… significantly… from Technical Manager to Associate Security Consultant. That was terrifying, but I was also so excited. After over 2 and a half years of hard work, I had finally achieved my dream!
Hell yeh! I’m a professional hacker now!
Imposter syndrome kicked in about 15 minutes into my first shift. What if I failed? What if I sucked? But the owners and the team were super supportive and have been ever since.
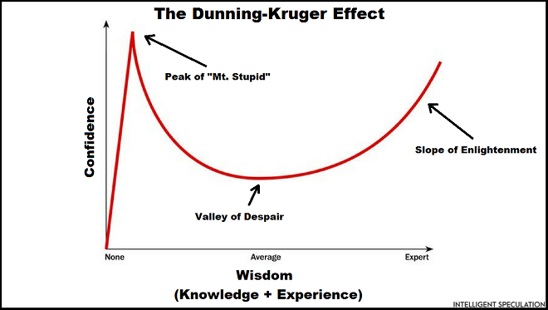
So what did I learn?
The most interesting thing about the whole hiring experience was being told that I was hired, not because of my hacking training and my glorious CEH certification, but rather because of my personal skills. The ability to talk to clients, to explain technical concepts in English. The skills that I wasn’t expecting to matter much were the deciding piece. I realised later that I should have known better. I did enough hiring myself to know that technical skills are almost never the deciding piece when looking for new staff.
I think it was this fact, more than anything else that inspired me to write this series. People put a lot of stock in technical skills; thinking that if they can just prove themselves by being able to do this next thing, they will get a job. But employers (mostly) don’t care about that. Technical skills can be taught, that’s what training budgets are for, whereas personal skills are often self-taught. Forged by experience and possibly, for a lucky few, talent. These skills are not so easily obtained but are the fundamental difference when working with clients. And ultimately, it’s the client who pays your wages.
Highlighting those skills more prominently in my CV would have been more advantageous than my technical skills, which were implied by the experience and certifications listed elsewhere.
I do not, however, regret the choices that I made, as they lead to a role with the best pentesting team in Australia (as voted by internal staff poll). I only highlight them now to help others to find their dream role sooner.
On the next episode…
In the next post I go over how the role of pentester differed from my preconceived image, and how a better understanding of what the role involves would have better prepared me for applications and the transition.
Next: Part Two - Great expectations
About the author
Nathan is certification addict, he can’t stop and it’s becoming a problem. We can’t talk to him about it directly but consider this a call for help.
If you need help with your security,
get in touch with Volkis.
Follow us on Twitter and
LinkedIn